Microsoft is adding extra warning screens to Windows 10 and Windows 11 to make Remote Desktop Protocol files harder to abuse, a move that directly targets a phishing trick already used in the wild by the Russian state-sponsored group APT29. The update ships with the April 2026 cumulative releases and is aimed at one of those threats that sounds boring until it empties clipboard contents, local drives, and credentials into the wrong hands.
The basic problem is simple: an RDP file can auto-configure a remote connection, which is handy for administrators and a gift for attackers. Open a malicious one and your PC can start talking to an attacker-controlled server before you have time to blink, which is a pretty ugly failure mode for something that looks like a plain file.
What changes when you open an RDP file
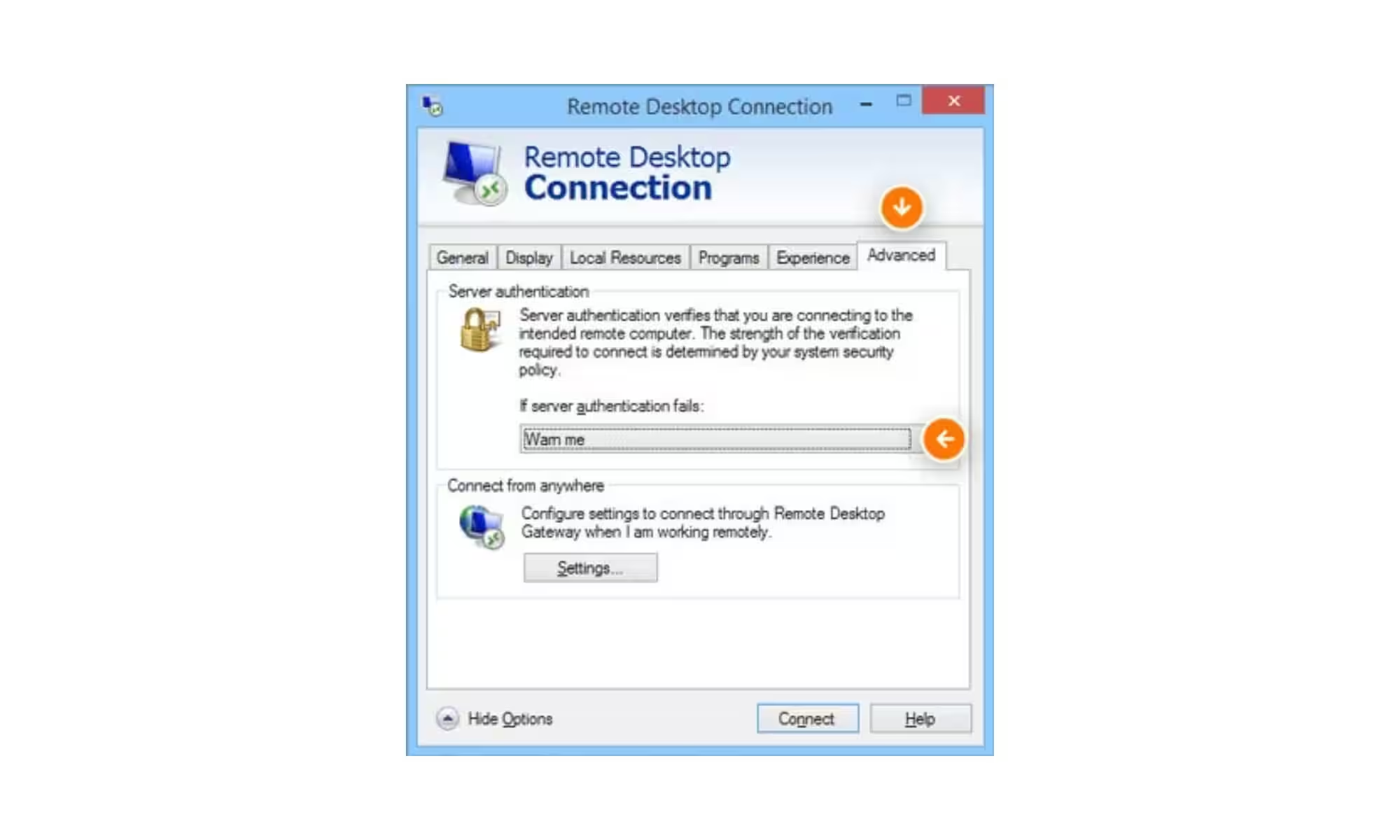
The first time you open an RDP file after installing the update, Windows shows a one-time educational prompt explaining what the file does and why it can be risky. After that, every direct RDP file launch brings up a security dialog before any connection starts.
That dialog is more useful than the usual security theatre. It shows whether the file is digitally signed by a verified publisher, reveals the remote address, and lists any local resources the file wants to redirect, including drives, clipboard access, and connected devices. Those redirections are off by default, so nothing gets shared unless you actively allow it.
Why Microsoft is targeting this attack
Microsoft is not reacting to a theoretical risk. Attackers have already used rogue RDP files in phishing campaigns, because files still feel harmless to a lot of people and that instinct gets exploited constantly. Security teams have spent years warning about malicious documents and attachments; the remote desktop file is just the next quiet little trap in the same family.
There is also a broader industry pattern here. Operating-system vendors increasingly prefer to put friction in front of risky workflows rather than hope users read a policy page, and that usually works better than the old ”trust us” approach. Microsoft is keeping that friction off the standard Remote Desktop client, though, so this only affects people who open .RDP files directly.

What IT admins can and cannot turn off
Administrators can temporarily disable the warnings through a registry key, but that option looks more like an escape hatch than a recommendation. In environments where remote access is routine, the new prompts may slow down a few legitimate workflows, but that is a fair trade if it stops a single credential theft chain from succeeding.
The likely next step is predictable: attackers will keep trying to find ways around user education, while Microsoft and other platform vendors keep adding guardrails directly into the file-opening experience. The annoying dialog may be the point.

