Windows users who rely on VeraCrypt may soon have a very unglamorous problem: their PCs could stop booting. The warning comes from VeraCrypt developer Mounir Idrassi, who says Microsoft terminated the account he has used for years to sign Windows drivers and the bootloader, cutting off the update path that keeps encrypted systems working on Microsoft’s platform.
Idrassi says he got no explanation and no appeal route, and that he could not reach a human at Microsoft. The immediate danger is not that VeraCrypt has suddenly become unsafe, but that Microsoft controls a key part of the signing process needed for Windows builds, which means a third-party encryption tool can be squeezed by platform rules even when the software itself is open source and widely used.
Why VeraCrypt users on Windows are exposed
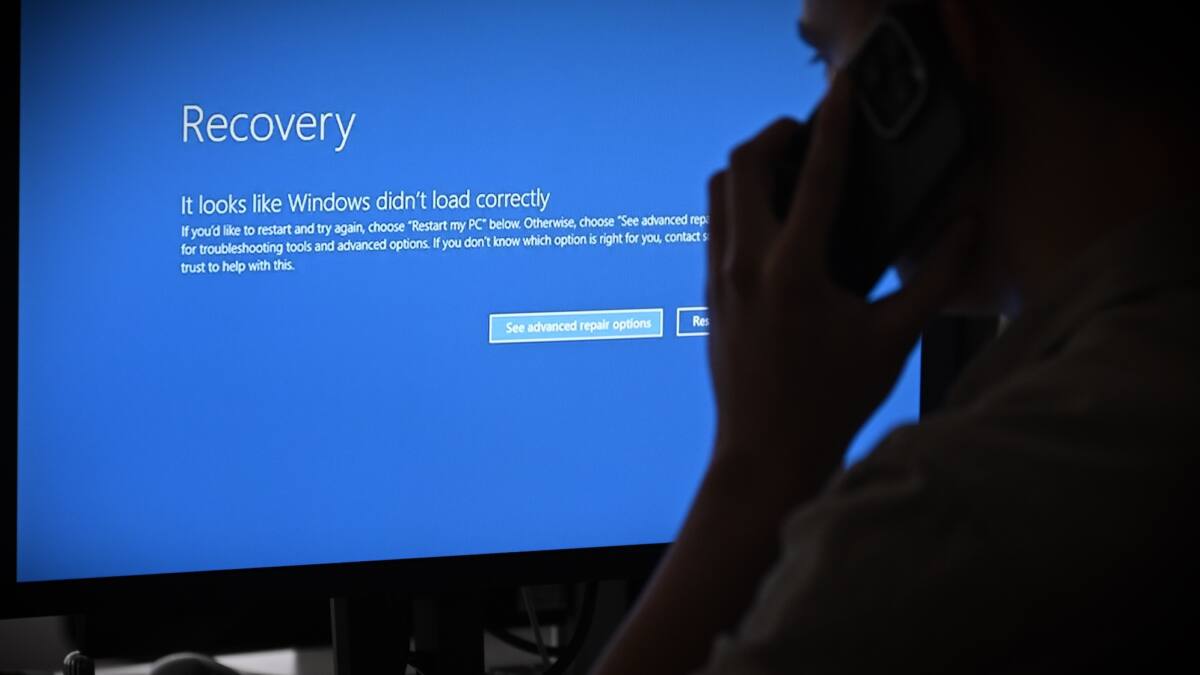
VeraCrypt lets users encrypt files or lock down an entire operating system before Windows loads, protecting data from pre-boot attacks. That full-disk mode is exactly why this matters: if the bootloader signature cannot be refreshed, affected systems may eventually fail during startup rather than just miss an ordinary app update.
Idrassi said he can still ship updates to Linux and macOS users, but most of his audience is on Windows and currently cannot receive them. The latest Windows release, published in May 2025, has nearly a million installer downloads, a reminder that this is not a niche inconvenience for a handful of hobbyists.
- VeraCrypt can encrypt individual files or an entire operating system.
- Windows updates depend on Microsoft account access for signing drivers and the bootloader.
- Idrassi says boot issues could begin around late June if the problem is not fixed.
Microsoft account lockout is the real choke point
This is not just a VeraCrypt problem. It is another reminder that software distribution on major platforms still runs through private gatekeepers, and those gates can close fast. Apple users have seen their own account suspensions turn into public headaches too, which is a cheerful little tradition nobody asked for.
Idrassi told TechCrunch that if the issue is not resolved in time, ”it would essentially mean a death sentence for VeraCrypt.” That is dramatic, but the underlying point is plain enough: encryption tools are only as durable as the signing and account infrastructure behind them, and users rarely get a say in that bargain until something breaks.
What affected Windows users should watch next
For now, Idrassi says users do not need to do anything special and that VeraCrypt continues to work. The clock is still ticking, though, because he says Microsoft will soon revoke the certificate authority used to digitally sign the software, and without a fresh signature the Windows boot path could start failing in the months ahead.
If Microsoft reverses course, this becomes a noisy but survivable platform dispute. If it does not, the bigger story will be how many security tools depend on accounts that can be switched off without warning, and how long users are supposed to trust ”open source” when the most important keys sit elsewhere.