In a stunning brush with digital disaster, a secret backdoor buried within a core compression utility almost handed hackers a master key to the internet’s most fundamental remote access tool: SSH. This vulnerability, hidden for two years in widely used Linux distributions, could have enabled attackers to log into countless servers without authentication. It was discovered only thanks to an eagle-eyed Microsoft researcher who spotted unusual slowdowns during an SSH session, revealing a threat that quietly lurked beneath the surface of everyday technology.
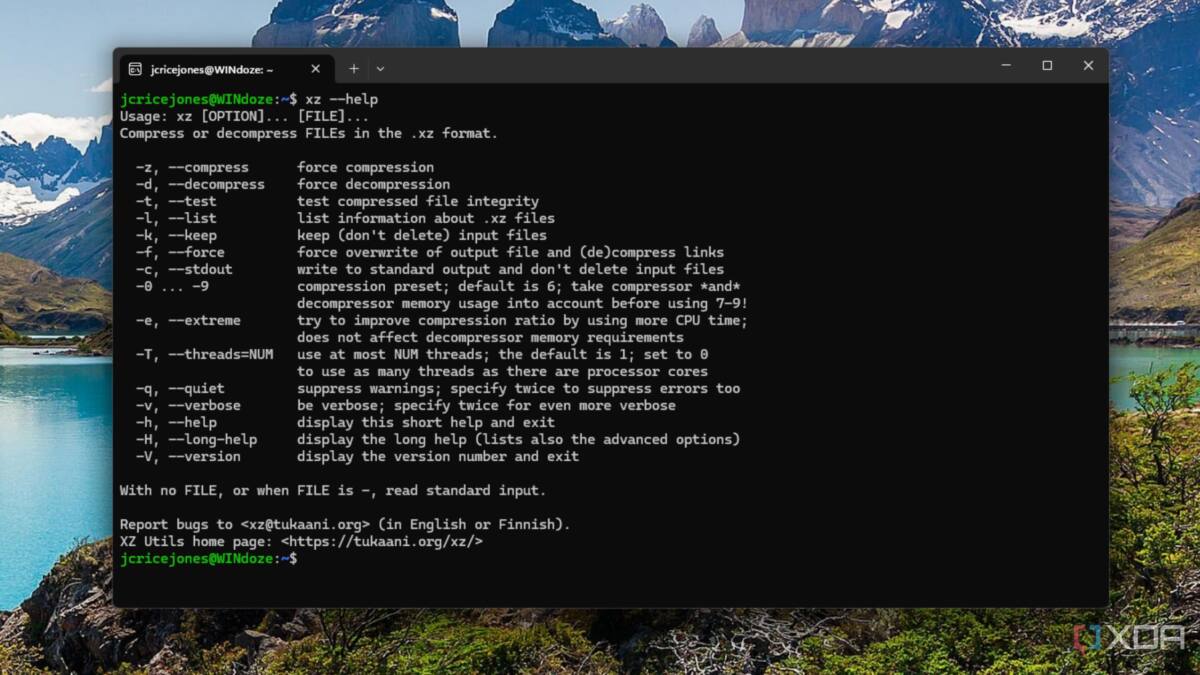
SSH, the secure shell protocol essential for remote server management across Linux, Windows, and just about every connected system, depends on XZ Utils for compression tasks. This dependency, usually invisible to end users, became the internet’s weak link. A malicious patch inserted into XZ Utils’ compression library, liblzma, quietly granted remote code execution through SSH without any valid credentials-a digital skeleton key that could have dismantled secure communications, stolen data, and disrupted countless services.
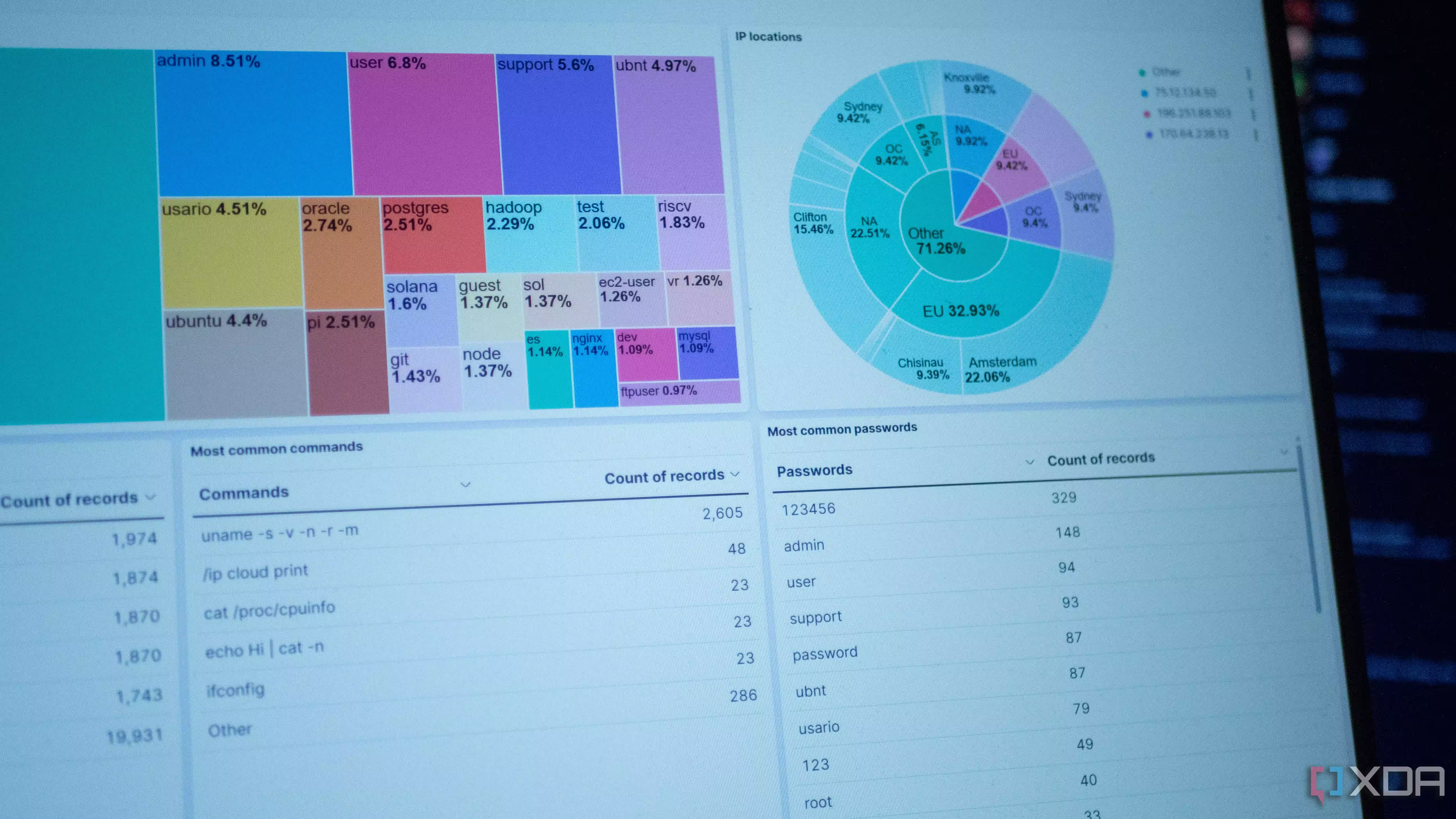
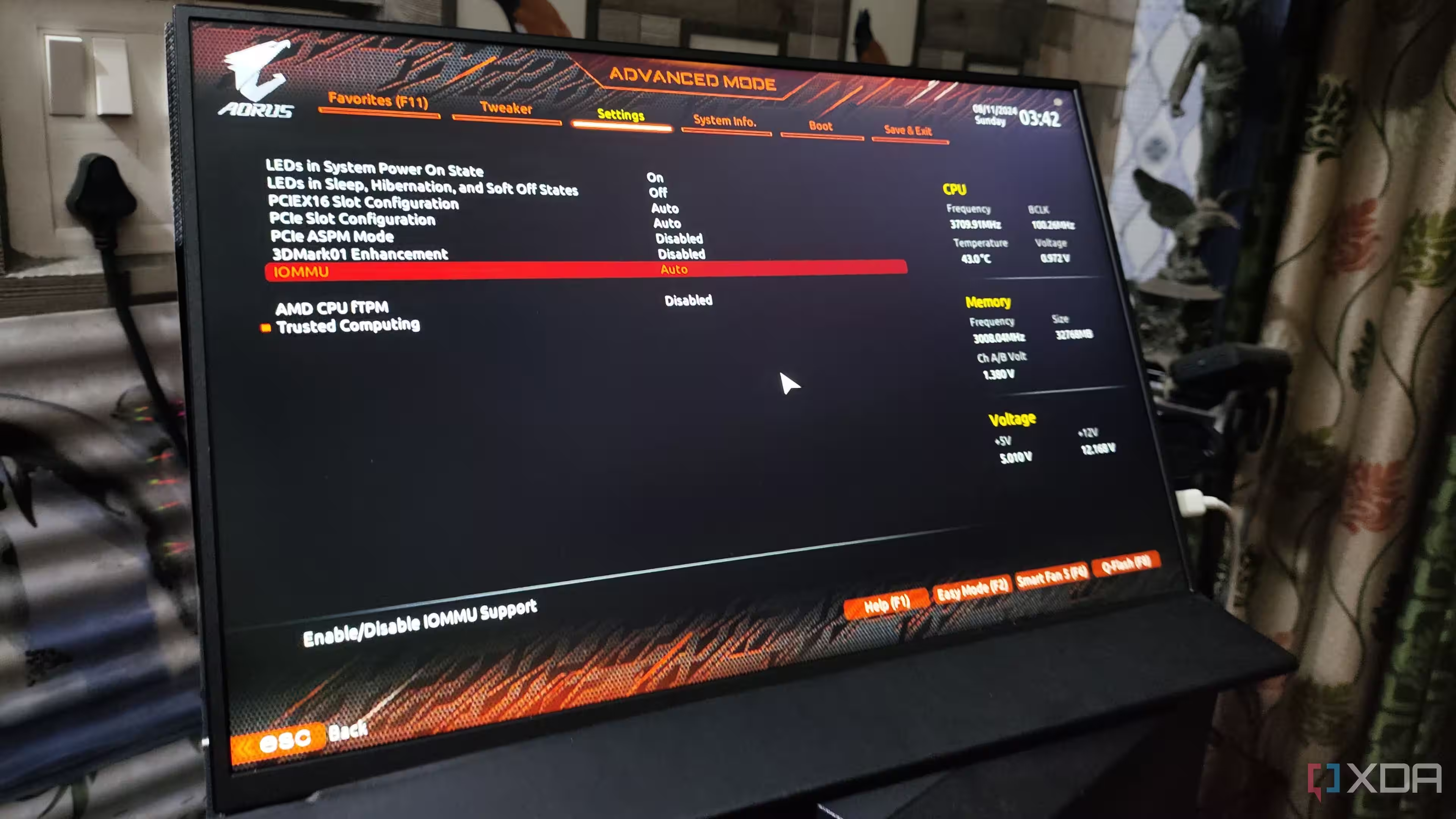
The attacker, a developer trusted by the open-source community, managed to earn control over essential aspects of XZ Utils’ maintenance. By exploiting this position, they inserted two malicious releases outside the public source control, which gradually infiltrated major Linux distributions like Fedora and various DEB-based systems. Their stealth craftsmanship included multi-stage payloads and cleanup routines that masked the backdoor’s presence, with the only symptom being marginal CPU spikes during SSH sessions.

This incident exposes a profound vulnerability in the open-source ecosystem’s decentralized model. Linus Torvalds’ famed ”Linus’s Law” asserts that with many eyes on the code, bugs become easy to spot and fix. Yet here, a critical component relied solely on the labor of one unpaid maintainer juggling the immense pressure of providing a backbone tool for global infrastructure. When the maintainer received persistent pressure to hand over control, the ecosystem’s blind trust turned into its Achilles’ heel.
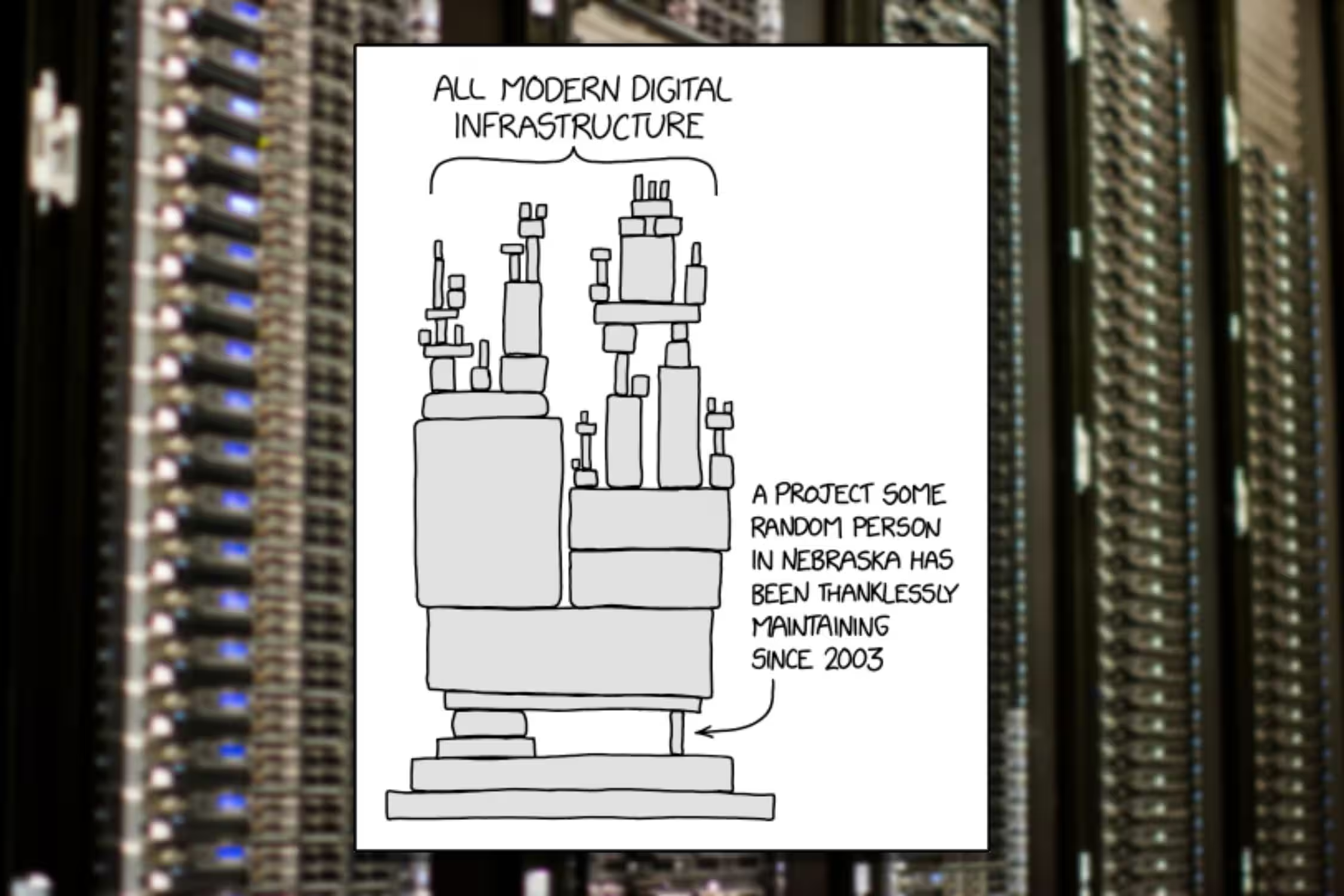
In an industry that profits heavily from free, open-source components, the security fragility exposed by the XZ Utils backdoor underlines a growing dilemma. How long before another critical but understaffed project falls prey to sabotage, accidentally or maliciously? Moreover, the lack of funding often leaves projects vulnerable to social engineering attacks and developer burnout, creating ripe conditions for covert compromises that might go unnoticed-until it’s too late.
The sophisticated nature of the attack hints at a state-sponsored figure behind it, utilizing both advanced technical methods and social engineering to infiltrate the software supply chain. Although the backdoor has now been patched, the identity of the culprits remains unknown, and the broader challenge persists. Without systematic support and better oversight on crucial open-source projects, the entire internet infrastructure remains at risk of a repeat scenario, potentially with even more devastating consequences.
This near miss is a stark reminder that the security of the vast digital web depends not only on flawless code but also on the often overlooked small teams and individuals who keep the wheels turning. The future of internet security requires rethinking how essential software maintenance is funded and managed-because the next catastrophe might not have a lucky researcher stumbling onto it in time.