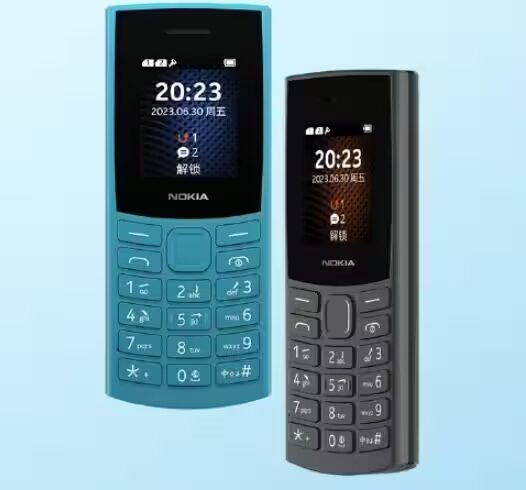
Russian mobile operator MegaFon has detected malicious software embedded in the firmware of several Nokia 105 and Nokia 106 (DUAL) feature phones. Around 280 devices were affected, most likely fake or modified versions rather than official models.
The investigation kicked off after unusual network traffic was spotted: these basic-feature phones were exchanging data patterns not typical for such simple devices. Neither regular SIM card functions nor standard phone operations could explain the strange transmissions.
How the malware on Nokia 105 and 106 operates
The malicious code is embedded directly into the phone’s firmware and activates immediately upon connecting to the mobile network. It communicates with a remote control server, ready to receive commands from attackers, all without leaving traces in device memory or logs.
The malware’s primary function is covert interception of incoming SMS messages. This allowed hackers to hijack victims’ phone numbers and register Telegram accounts without the users’ knowledge.
Impact and protective measures for users
Standard user actions like resetting or rebooting the phone are ineffective against this malware since it’s baked into the firmware ”out of the box” and operates independently of owner intervention. MegaFon emphasized that only a small subset of devices with altered firmware were compromised-not the entire Nokia 105 and 106 lineups.
Thanks to its internal monitoring systems, MegaFon quickly identified the infected devices and blocked their communication with the control servers, preventing further attacks on subscribers.
Why this matters to the feature phone market
At first glance, affordable feature phones are seen as simple and secure gadgets, far removed from the sophisticated threats targeting smartphones. However, this incident reveals that counterfeit or tampered budget phones have become a new playground for cybercriminals. Manufacturers, carriers, and buyers alike must be vigilant about device authenticity and security.
In the broader context of rising cyberattacks on IoT devices and low-cost gadgets, the Nokia 105 and 106 malware case underscores a critical point: even a cheap device with basic functions can be exploited for hidden data collection and remote control.
For Russian readers, it’s especially worth noting MegaFon’s role as one of the country’s largest telecom operators, whose proactive detection helped mitigate wider impact-highlighting the increasingly sophisticated cyber risks targeting even the most basic devices in the Russian market.
From a global perspective, this situation reminds us that no device is too simple to be ignored by attackers. As IoT and inexpensive devices proliferate, they present a growing attack surface. This makes it crucial for the international tech community to prioritize security in all connected hardware, not just high-end smartphones or computers.